Last updated on December 20, 2022
Volume 03 Issue 12- 20th December 2022

Business Email Compromise

In Business Email Compromise (BEC), an attacker gets access to a business email account and tries to copy the owner’s identity. This is done to trick the company, employees, customers or partners. Even technology giants have fallen due to these types of serious threats and attacks. This is also known as “man in the email attack”.

- Do you know that 200 years have passed since Charles Babbage built the world’s first computer, the Difference engine (1822)?
https://en.wikipedia.org - Cybercrime To Cost The World 8 Trillion Annually In 2023 – Cybercrime is predicted to cost the world $8 trillion USD in 2023, according to Cybersecurity Ventures. If it were measured as a country, then cybercrime would be the world’s third largest economy after the U.S. and China.
https://cybersecurityventures.com - 68% of surveyed people agree or strongly agree that social media has made them jealous of other people’s lives
https://www.digitalinformationworld.com - 76% of US Consumers Prefer Smartphones for Online Shopping
https://www.digitalinformationworld.com

Top 3 things to protect yourself
- Update your devices to protect important information (software / firmware)
- Protect your accounts with multi-factor authentication
- Back up data regularly to the cloud or an external hard device

Google Releases Security Update for Chrome Zero Day
Google has released a security update to address a High severity zero-day vulnerability tracked as CVE-2022-4262.
https://digital.nhs.uk
Alert (AA22-321A) – #StopRansomware: Hive Ransomware
This joint Cybersecurity Advisory (CSA) is part of an ongoing #StopRansomware effort to publish advisories for network defenders that detail various ransomware variants and ransomware threat actors.
https://www.cisa.gov
BD BodyGuard Pumps Vulnerability
CISA Advisory includes a missing protection mechanism for alternate hardware interface vulnerability that could allow an attacker to change configuration settings or disable the pump.
The BD BodyGuard™ infusion pump is a small, lightweight ambulatory infusion pump which offers flexibility and reliability. Effortless transition between hospital and home care requirements is the core of the BD BodyGuard™ infusion pump.
https://digital.nhs.uk
Critical severity vulnerability in Fortinet FortiOS SSL-VPN
This Alert is relevant to organisations who deploy FortiOS to facilitate remote access for their users. The Alert is intended to be understood by slightly more technical users who maintain systems – there is no action for the end users to take.
https://www.cyber.gov.au

Cyber News
Top passwords used in RDP brute-force attacks
Specops Software released a research analyzing the top passwords used in live attacks against Remote Desktop Protocol (RDP) ports.
https://www.helpnetsecurity.com
Chinese threat group spoofs Coca-Cola and McDonald’s in sophisticated phishing campaign
A new large-scale phishing campaign with over 42,000 unique domains impersonates popular brands to spread malware, threat intelligence company Cyjax discovered.
https://cybernews.com
5G can reduce – but also create – security risk
In this article, learn about the most common 5G security misconceptions, how to make sure the network is safe, but also how 5G can benefit businesses.
https://www.helpnetsecurity.com
90% of organizations have Microsoft 365 security gaps
A recently published study evaluated 1.6 million Microsoft 365 users across three continents, finding that 90% of organizations had gaps in essential security protections.
https://www.helpnetsecurity.com

He could not stand it anymore…..

Ayesh was studying for a higher Diploma course at a famous institute. It was his dream to start higher studies at this institute since he had a target to continue up to the Degree after the higher Diploma and he very well knew that this institute would recommend him to a good working place too.

Awareness Programmes
Past Events:
- An introduction session about Hithawathi Project was held on the 24th November 2022 at Galle Face hotel at the LKNOG 6th event.

- An awareness session of Hithawathi was held on 18th November 2022 at Joomla training workshop at Kandy Mahamaya College – which was organized by Nenasala Teldeniya. There were about 45 students participated for this session..

To join future webinar sessions and learn about cyber security, please Join the Viber or WhatsApp group below:



Movie Hint
War Games – 1983
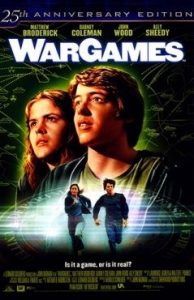
War Games was one of the first hacker films to be released in 1983. It’s main character is David. A lazy high school student who has happens to be a computer prodigy. He comes upon a system that doesn’t identify itself but allows him to play games………
https://www.youtube.com/watch?v=hbqMuvnx5MU
 GADGET
GADGET
Christmas Ornament made from PCB

An enjoyable Christmas-themed project that involves PCB art used for the decoration of the Christmas tree.
https://www.hackster.io/Arnov_Sharma_makes/christmas-ornament-made-from-pcb-12533c




