Last updated on July 1, 2024
AI in Cybersecurity
Last updated on August 20, 2024 Artificial Intelligence (AI) in cybersecurity involves using AI technologies to improve the protection of digital systems and data from cyber threats. AI uses methods like machine learning and neural networks to better detect, prevent, …
Message from your Big Boss
Last updated on June 24, 2024 Don’t we all feel a bit tense and try to respond quickly when we get an email from our big boss? Cybercriminals have become very skilled at exploiting this behavior through a tactic known …
Would you let the piggybackers in?
Last updated on April 18, 2024 What is Piggybacking? Piggybacking means sneaking past security measures by using an authorized person’s permission or access. It’s a huge problem for both physical and online security. Organizations and the general public need to …
Worried about your close-ups?
Last updated on March 20, 2024You may not be able to reverse but there is a hope to move forward. Source of the image: https://stopncii.org/ StopNCII.org is run by the Revenge Porn Helpline, which is a part of …
Spoofers Tricking our Brain
Last updated on February 20, 2024 What is Brainjacking? Doctors worldwide use brain implants for disabled patients specifically when treating patients with Parkinson’s disease, chronic pain, tremor and muscle spasms. Brainjacking is a cyber attack done by hacking the brain …
The silent threat of ‘Cryptojacking’
Last updated on January 19, 2024 What is Cryptojacking? Cryptojacking is a form of cybercrime which involves access to peoples’ devices (computers, tablets, smartphones, and servers) in an unauthorized manner by cybercriminals to mine cryptocurrency. Similar to other cybercrimes the …
Shop… shop… shop. till you drop, this festive season
Last updated on December 19, 2023 Online shopping is easy but ……. Is online shopping associated with a risk? Online shopping is simple, but it can be risky. When you buy things online, there’s a chance that cybercriminals might try …
Non-Consensual Intimate Images
Last updated on January 4, 2024“Nonconsensual intimate images” refer to suggestive graphic images that are shared without the consent of the person/s who appear therein. Most of the time these are leaked to take revenge or to create a bad …
Your trash is a treasure for someone….
Last updated on August 18, 2023 Trash can be of two forms: physical trash and digital trash. ‘Dumpster diving’ in its simplest meaning is the act of looking through others’ trash to find information that might be useful. The ultimate …
Black Hat, White Hat and Grey Hat
Last updated on August 28, 2023 Who are Hackers and what is the Hat system? Hackers are individuals who have the knowledge and expertise to breach cyber defence systems. In cybersecurity, hackers are classified as per a Hat system which …
Are U being bullied Online?
Last updated on June 19, 2023 What is Cyberbullying? Bullying with the use of digital technologies is known as cyberbullying. This may take place over digital devices like mobile phones, computers and tablets through messaging apps, social media, forums and …
ChatGPT in the limelight
Last updated on June 8, 2023ChatGPT in the limelight What is ChatGPT? ChatGPT is an artificial intelligence (AI) chatbot created by OpenAI for online customer care. This runs on a language model called Generative Pre-trained Transformer (GPT). It is pre-trained …
Software Firewalls
Last updated on April 4, 2023 What is a software firewall? A software firewall is a special computer software that runs on a computer or a server. Its main purpose is to protect the computer or server from outside attempts …
Common IoT attacks
Last updated on April 4, 2023 What is the Internet of Things (IoT)? IoT means a lot of physical devices around the world which are connected to the internet or other communication networks with embedded technologies to collect and transmit …
5G
Last updated on July 20, 2021What would be the next? It is a simple law that when technology becomes more and more advanced the misuse of it and subsequently the security issues also increase. This fact is about technology versus …
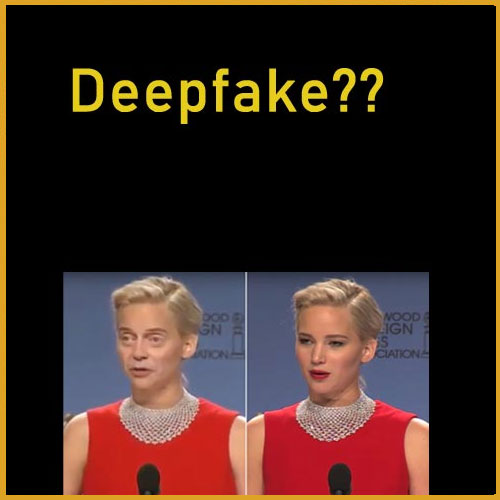
Deepfake
Last updated on July 21, 2021As defined by Wikipedia, “Deepfakes are media that take a person in an existing image or video and replace them with someone else’s likeness using artificial neural networks. They often combine and superimpose existing media …
How to tell if an e-mail is a scam
Last updated on October 17, 2022Among the e-mails you receive daily in different forms, it is not easy to identify whether it is a genuine or a scam email. The following indicators will help you to recognize fraudulent e-mails. Incomplete …
Safety on Your Email
Last updated on August 15, 2021Tips to strengthen security on your email It is really difficult to find a person who doesn’t know of Email or electronic mail. Also it is even difficult to find a person who doesn’t have …
Identify Computer Virus
Last updated on August 14, 2021 What is a Computer Virus? A computer virus is a small program that can be spread from one computer to another and can even affect a computer’s operations. Such viruses can modify or destroy …