Last updated on November 29, 2022
Volume 02 Issue 12 – 20th December 2021

Covid-19 Cyber Threats
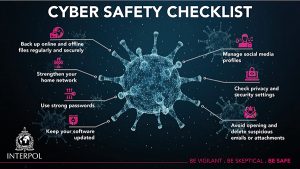
Cyber threats are constantly evolving in order to take advantage of online behaviour and trends. The COVID-19 outbreak is no exception.
Cybercriminals are attacking the computer networks and systems of individuals, businesses and even global organizations at a time when cyber defences might be lowered due to the shift of focus to the health crisis.

- Cybercrimes in Sri Lanka double in 2020
https://www.themorning.lk/ - Users Between the ages of 12 and 17 prefer TikTok to Instagram.
https://www.digitalinformationworld.com/ - The number of smartphone subscriptions worldwide today surpasses 6 billion
https://www.statista.com/ - 2.9B people (estimated 37%) still offline, while 4.9B used internet in 2021
https://www.aa.com.tr/en/world/

06 Credit Card Scams
Here are six common scams – to avoid becoming a victim of fraud. (based on o an article published on Forbes)
- Overcharge Scams
- Interest Rate Reduction Scams
- Arrest Phone Call Scams
- Donation Scams
- Skimming
- Phishing Scams

Apple iMessage “ForcedEntry” Vulnerability
Using “ForcedEntry” vulnerability, an attacker could execute an arbitrary code on the device and gain access to the device.
https://www.cert.gov.lk/view?lang=en&articleID=263
Ethical hackers and the economics of security research
Bug crowd released a report which provides CIOs and CISOs valuable insight on ethical hackers and the economics of security research. New findings indicate a startling shift in the threat landscape with 8 out of 10 ethical hackers recently having identified a vulnerability they had never seen before.
https://www.helpnetsecurity.com/2021/11/22/ethical-hackers-security-research/
FBI system hacked to email ‘urgent’ warning about fake cyberattacks
The Federal Bureau of Investigation (FBI) email servers were hacked to distribute spam email impersonating FBI warnings that the recipients’ network was breached and data was stolen.
https://www.bleepingcomputer.com/news/security/fbi-system-hacked-to-email-urgent-warning-about-fake-cyberattacks/

Cyber News
Millions of devices at risk from newly revealed Log4j software vulnerability
Hundreds of millions of devices around the world could be exposed to a newly revealed software vulnerability. The threat is so large, a senior Biden administration cyber official warned executives from major US industries.
https://7news.com.au/technology/millions-of-devices-at-risk-from-newly-revealed-log4j-software-vulnerability-c-4940332
Over 50,000 European business users exposed in a data leak
According to the researchers, the leak exposed more than 300,000 records in a 500MB dataset. The breach is likely to affect 50,000-150,000 ecommerce buyers and sellers.
https://cybernews.com/news/over-50000-european-businesses-users-exposed-in-a-data-leak/
Top 5 cybersecurity considerations for file uploads of vaccination records
As vaccination mandates become more common, immunization records are increasingly required across the world. Organizations are turning to the digital space to upload images of COVID-19 record cards as electronic proof of vaccination.
https://www.helpnetsecurity.com/2021/11/22/file-uploads-vaccination-records/
Research Shows That Sensors Integrated Into Smartphones Can Be Used In Order To Point Out Spy Cameras
Smartphones nowadays have technology that can be utilized in order to identify other, hidden spy cameras.
https://www.digitalinformationworld.com/2021/11/research-shows-that-sensors-integrated.html
China’s New Data Protection Policy Could Serve as a Lesson for the U.S.
China’s new Personal Information Protection Law (PIPL) was recently implemented, and the legislation will have a significant impact on private data protection, both in China and worldwide.
https://www.digitalinformationworld.com/2021/11/chinas-new-data-protection-policy-could.html

WhatsApp Ban On The Bad Group!

One day Himali sent Hithawathi a chat via WhatsApp;
Himali: Miss, I had an affair with someone two years ago and recently I heard that he has shared my pictures edited on a WhatsApp notorious group, where people talk about women and sex……

Awareness Programmes
Past Events:
- An awareness sessionwas held on 09th December 2021 at SLFI, at the Training programme on “Tips to manage cyberbullying and prevent harm”. This was organized by Ministry of Health – (1926 helpline) for the counsellors of District hospitals and health professionals.
- Hithawathi organised a webinar session on “Blackmailing in Cyberspace for the sake of love” on Saturday 18th December 2021 via zoom, FB live and live streamed through Hithawathi YouTube channel. The targeted audience was young girls and women. It was an interactive session.
To join future webinar sessions and learn about cyber security, please Join the Viber or WhatsApp group below

Movie Hint
Unfriended: Dark Web

Unfriended: Dark Web is a 2018 American computer screen horror film written and directed by Stephen Susco in his directorial debut.
When a teen finds a laptop with a cache of hidden files, he and his friend discover that the previous owner has access to the dark web and is watching over them.
https://youtu.be/XenTM_C9fxM
 GADGET
GADGET
Tiny drones with fluttering wings developed by US Air Force
A team of researchers inside the US Air Force Research Lab have also developed capabilities that allow the drone to swivel its head, where a camera sits recording who is where and doing what.


Hithawathi WhatsApp & Viber Number
+94 77 771 1199
(during our business hours – Weekdays 08.30 am – 07.00 pm
Saturdays 08.30 am – 05.00 pm )

Comment the correct answer and win a data card from Hithawathi by visiting our Facebook page every Friday, Saturday & Sunday.