Last updated on January 20, 2022
Volume 03 Issue 01 – 20th January 2022

Morphing

The word morph comes from the Greek word “metamorphosis,” which means to transform. Morphing refers to smooth transformation of images.
For example – Transforming an image of a rabbit to a dragon
Morphing effects have improved a lot over the years and are more driven towards creating less obvious effects that appear to be more realistic.

- Who is the mother of Wi-Fi? Hedy Lamarr (1914-2000) was an Austrian-born American film actress and inventor.
- 93% of Tested Networks Vulnerable to Breach
https://securityboulevard.com/2022/01/93-of-tested-networks-vulnerable-to-breach/ - Report: 60% of U.S. infosec professionals believe ransomware is as serious as terrorism
https://venturebeat.com/2022/01/01/report-60-of-u-s-infosec-professionals-believe-ransomware-is-as-serious-as-terrorism/ - Estimated value of cyber insurance premiums worldwide in 2025 20bn USD
https://www.statista.com/markets/424/topic/1065/cyber-crime-security/#overview

New Year’s tech resolutions 2022
- Upgrade your infrastructure
- Get out of your echo chamber
- Embrace proactive healthcare
- Reduce your carbon footprint
- Simplify your life

Remote Code Execution vulnerability in Apache Java logging library (Log4j)
A critical vulnerability was found in the Java logging library log4j which allows an attacker to perform Remote Code Execution (RCE).
https://www.cert.gov.lk/view?lang=en&articleID=264
Silicon Labs Z-Wave chipsets contain multiple vulnerabilities
Various Silicon Labs Z-Wave chipsets do not support encryption, can be downgraded to not use weaker encryption, and are vulnerable to denial of service. Some of these vulnerabilities are inherent in Z-Wave protocol specifications.
https://kb.cert.org/vuls/id/142629

Cyber News
Google Releases Security Updates for Chrome
Google has released Chrome version 97.0.4692.71 for Windows, Mac, and Linux. This version addresses vulnerabilities that an attacker could exploit to take control of an affected system.
https://www.cisa.gov/uscert/ncas/current-activity/2022/01/05/google-releases-security-updates-chrome
Top DevOps Trends That Will Dominate in 2022
The future of DevOps looks very promising, do you agree with that? Well, the DevOps stats are saying so. Indeed, research by Global Market Insights shows some encouraging numbers for DevOps future: “DevOps Market size surpassed $4 billion in 2019, and is ready to develop at more than 20% CAGR between 2020 and 2026.
https://securityboulevard.com/2021/12/top-devops-trends-that-will-dominate-in-2022/
How will the cybersecurity industry evolve in 2022?
The cybersecurity landscape has always been dynamic. However, this past year highlighted vulnerabilities and attack vectors that will drive trends and shape global expectations for security in 2022.
https://www.helpnetsecurity.com/2021/12/28/cybersecurity-industry-2022/
Hackers use video player to steal credit cards from over 100 sites
Hackers used a cloud video hosting service to perform a supply chain attack on over one hundred real estate sites that injected malicious scripts to steal information inputted in website forms.
https://www.bleepingcomputer.com/news/security/hackers-use-video-player-to-steal-credit-cards-from-over-100-sites/

Mysterious Transactions From Bank Account

Lasitha was a school teacher and did private tuition classes. During his classes he used to switch off his mobile phone and check his emails /messesgs after the class. One day he was confused when he received several messages from the bank XYZ. That is the bank his all accounts are created.
Lasitha : I didn’t do any transaction, but why am I getting these messages from the bank 💭

Awareness Programmes
Past Events:
- Hithawathi conducted the second awareness session on “Tips to manage cyberbullying and prevent harm” at the Training programme held on 15th December 2021 at Sri Lanka Foundation Institute (SLFI). This was organized by Ministry of Health (1926 helpline) for the counsellors of District hospitals and health professionals. There were about 50 participants.

- Hithawathi conducted an awareness session at Suhuruliya Kalutara district forum organized by ICTA on 22nd December 2021. This was held at Mathugama Sanasa Bank Auditorium and about 50 ladies from Local communities participated.

To join future webinar sessions and learn about cyber security, please Join the Viber or WhatsApp group below

Movie Hint
The net 2.0
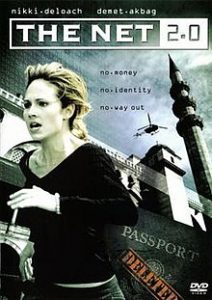
The life of a young computer systems analyst is thrown into turmoil when, after arriving in Istanbul to start a new job, she finds her credit cards useless, her bank account empty, and her identity stolen.
https://www.dailymotion.com/video/xl6arj?playlist=x1q109
 GADGET
GADGET
Arduglasses
Arduboy is an open source, handheld video game console that is built around an Arduino-compatible microcontroller. That Microchip ATmega32U4 controls the Arduglasses. They also run a lot of the software developed for the Arduboy —can even play games on these smart glasses!

Hithawathi WhatsApp & Viber Number
+94 77 771 1199
(during our business hours – Weekdays 08.30 am – 07.00 pm
Saturdays 08.30 am – 05.00 pm )

Comment the correct answer and win a data card from Hithawathi by visiting our Facebook page every Friday, Saturday & Sunday.





